Findings Staff Report | Oct. 12, 2020
Every day—often many times a day—we rely on cryptography.
It’s what keeps our bank accounts safe when buying online and allows our computers to do updates safely. Cryptography also assures confidentiality and authenticity in our emails and other forms of communication on the internet and other networks.
At its core, it is the art of writing or solving codes--to use mathematical tools to protect the secrecy and integrity of information in transition or storage.
Public key cryptography, the standard today, was invented in the 1970s to enable human beings to build a large and secure computer network. Our conventional computers can't break them.
However, these security methods are expected to be no match for the quantum computer, which, when and if created, could solve certain computational problems much more quickly, threatening the world’s ever-growing information-technology infrastructure.
Theoretically, this means there’s a need to develop new cryptographic algorithms that can resist quantum computer attacks, known in the scientific world as post-quantum algorithms.
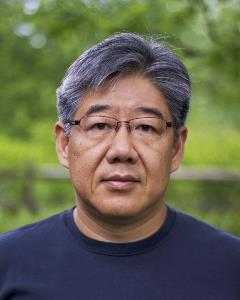
Enter the University of Cincinnati's Jintai Ding. Ding, who earned his Ph.D. in mathematics at Yale University in 1995, joined the UC faculty in 1998. In 2004, he created a cryptographic algorithm—called Rainbow—to stump a quantum computer.
Rainbow is now one of seven finalists in a competition to choose the post-quantum security standards for use on the post-quantum internet in the United States and beyond.
The National Institute of Standards and Technology, a non-regulatory agency of the United States Department of Commerce, issued its call for proposals in November 2017. Eighty-two submissions poured in from researchers around the world.
Rainbow has made it through three elimination rounds and is now one of three finalists in the Digital Signatures category. The four other finalists are in the Public-Key Encryption category. At the end of this “selection” round, the agency will decide on the small subset of these algorithms that will form the core of the first post-quantum cryptography standard. NIST plans to release the initial standard for quantum-resistant cryptography in 2022 to counter the future threat of quantum decryption.
“No one has been able to crack Rainbow,” says Ding, who puts the problem out there online for anyone to try to solve.
As Ding describes it, he “made the gamble” to switch his primary research from quantum algebra related to string theory to post-quantum cryptography in 2000. At the time, there was a lot of doubt in the scientific community as to whether a quantum computer could ever exist.
NIST’s call for proposals validates Ding’s suspicion that quantum computers aren’t that far off.
“The question of when a large-scale quantum computer will be built is a complicated one,” according to Project Overview by NIST. “While in the past it was less clear that large quantum computers are a physical possibility, many scientists now believe it to be merely a significant engineering challenge. Some engineers even predict that within the next twenty or so years sufficiently large quantum computers will be built to break essentially all public key schemes currently in use.”
Historically, it has taken almost two decades to deploy a modern public-key cryptography infrastructure, according to NIST—meaning, the time is now. The last selection phase is expected to take 12-18 months.
“I don’t think the public realizes how great the need is for this work,” says Ding, who will meanwhile continue building UC’s research strengths and expertise in post-quantum cryptography. “Our security, our privacy, our future digital lives depend on it.”